Tag: Gozi ISFB

Malspam Distributing Ursnif (Gozi ISFB)
A user received malspam with a .doc attachment. Static analysis of the file showed it was a Microsoft Word 2007+ document with an embedded macro located in vbaProject.bin. The malware authors trick victims into enabling macros (Enable Content) and, to better evade sandboxes, use AutoClose to execute the macro after the file has been closed. ...
HookAds Malvertising Redirects to RIG-v EK at 217.107.219.99. EK Drops Ursnif Variant Dreambot.
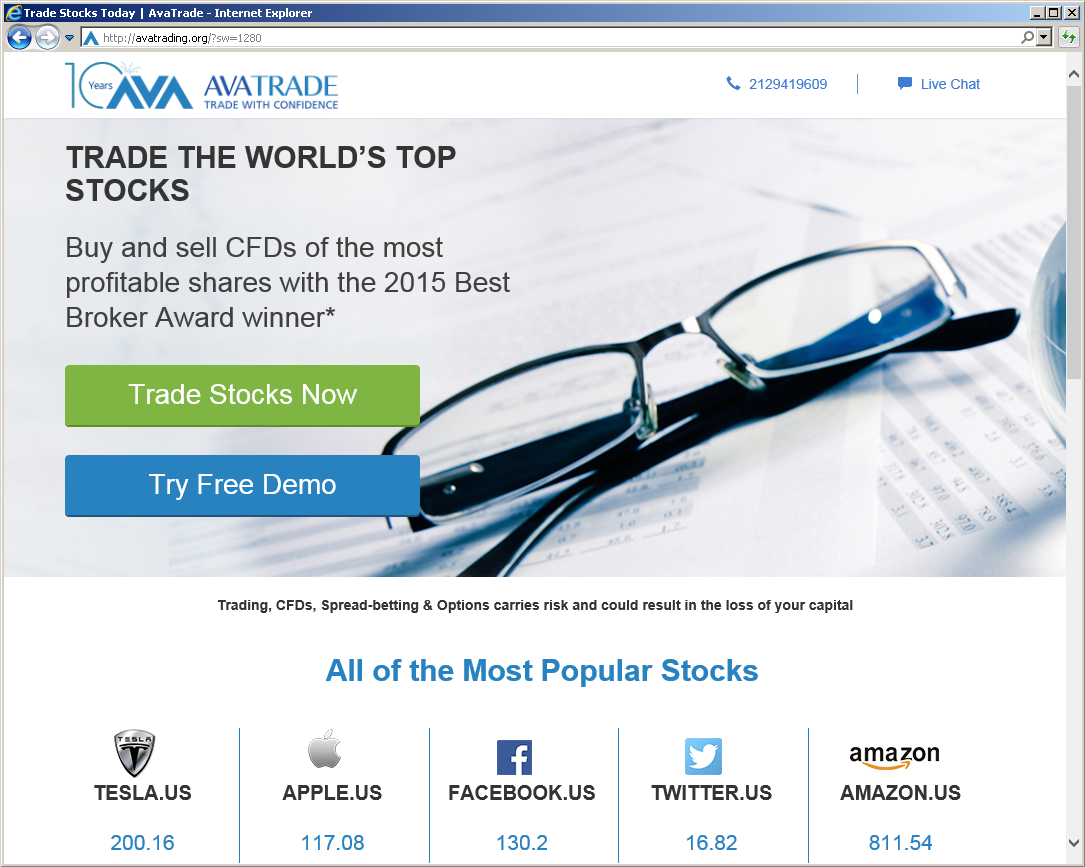
IOCs: 104.27.134.78 – multimediaz.net – Website hosting script for onclickads.net 206.54.163.4 – onclickads.net – Checks Flash. Redirects to onclkds.com. 206.54.163.50 – onclkds.com – Returns “302 Moved Temporarily,” new location is set to avatrading.org 185.51.244.202 – avatrading.org – Domain in fake ad network. Contains iframe for stockholmads.info 185.51.244.210 – stockholmads.info – GET /rotation/check-hits? – Contains iframe for RIG-v EK ...

EITest Leads to RIG-v EK at 185.159.130.122. Ursnif Variant Dreambot.
IOCs: 92.243.23.204 – www[.]caltech[.]fr – Compromised website 185.159.130.122 – more.THEBESTDALLASFLORISTS.COM – RIG-v EK 5.196.159.175 – GET /images/[removed]/KTDEi/.avi – CnC traffic 46.4.99.46 – GET /tor/t64.dll – ET CURRENT_EVENTS Possible Malicious Tor Module Download 37.48.122.26 – curlmyip.net – External IP lookup Post-Infection DNS Queries: resolver1.opendns.com – ET POLICY OpenDNS IP Lookup curlmyip.net 222.222.67.208.in-addr.arpa myip.opendns.com nod32s.com Traffic: Hashes: SHA256: 37f7e78080f85e6f98136e927a69a72ea7d619f230b476b5d6826ebc1eee29a0 ...